Satellite Post-Quantum Cryptography (PQC) [Strategy]
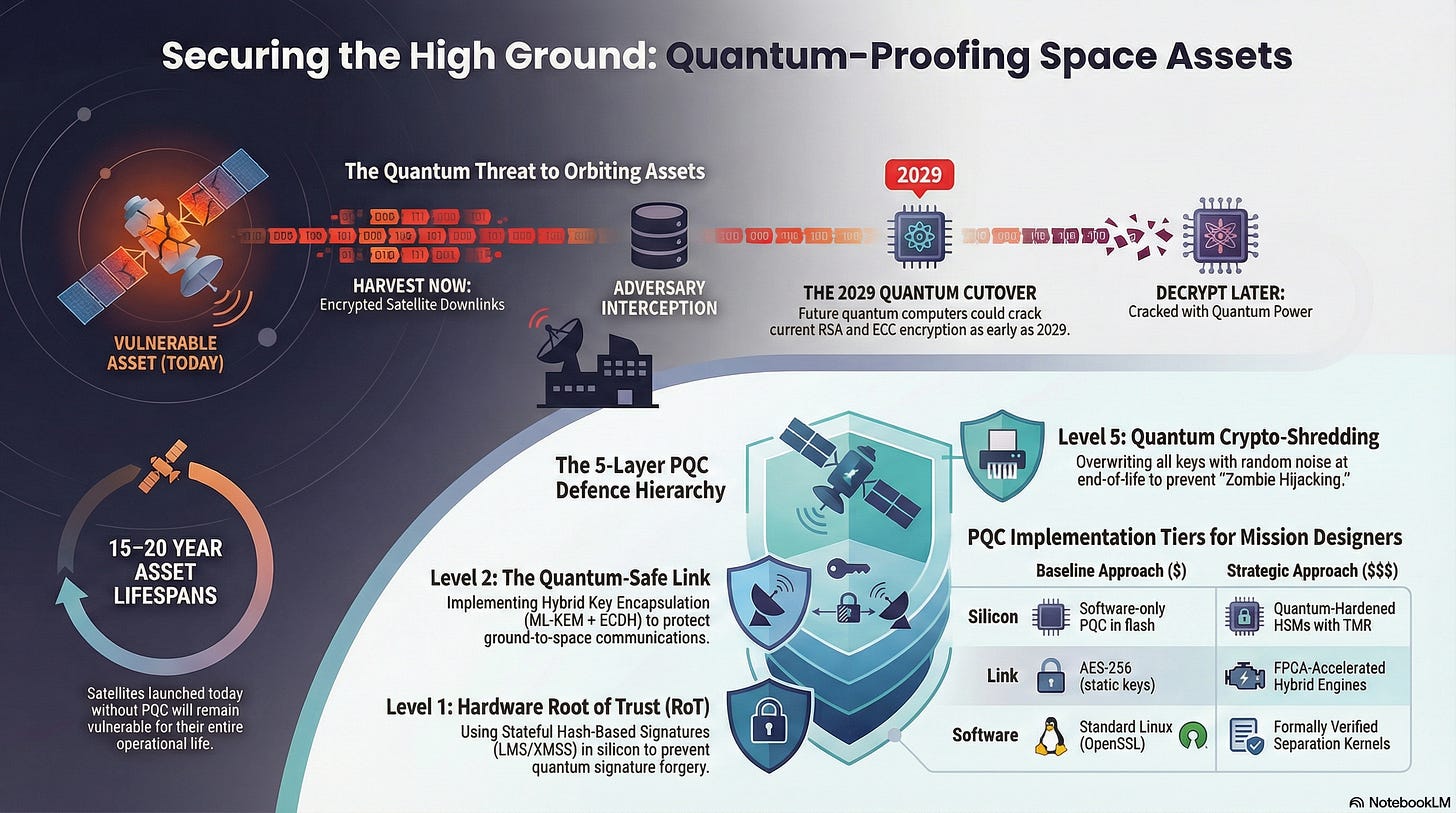
Adversaries may intercept satellite downlinks today, banking on the fact that future quantum computers will crack current RSA and ECC encryption as early as 2029.
The satellite industry is facing a “Harvest Now, Decrypt Later” (HNDL) threat.
Adversaries may intercept satellite downlinks today, banking on the fact that future quantum computers will crack current RSA and ECC encryption as early as 2029.
Because satellites can have operational lifespans of 15–20 years, a satellite launched today without Post-Quantum Cryptography (PQC) pose a significantly higher risk.
Securing the “High Ground” requires a shift from classical mathematics to lattice-based and hash-based primitives that can survive Shor’s and Grover’s algorithms.
I. The Hierarchy of PQC Strategy
1. Level 1: The Quantum-Resistant Foundation (Hardware & Boot Trust)
A satellite’s “Silicon-Birth” should now account for Shor’s algorithm. If the bootloader relies on classical RSA, a quantum-capable adversary could forge firmware signatures before the satellite even leaves the cleanroom.
The Vulnerability: Quantum Signature Forgery; using future quantum compute to crack the private keys used to sign the satellite’s immutable ROM.
The Technology: Stateful Hash-Based Signatures (LMS/XMSS).
Failure Consequence: Permanent “Quantum Rootkit” installation that survives all reboots and software wipes.
Progressive Security Actions:
Least Secure: Using RSA-2048 or ECC-256 for Secure Boot (vulnerable to HNDL).
Moderate: Software-defined PQC boot checks (ML-DSA) that are patchable but lack hardware-level isolation.
Most Secure: Hardware Root of Trust (RoT) using LMS/XMSS burned into Write-Once-Read-Many (WORM) memory, ensuring the initial “handshake” with the OS is mathematically immune to quantum attacks.
2. Level 2: The Quantum-Safe Link (Ground-to-Space Gateway)
This is where the “Harvest Now, Decrypt Later” threat is most acute. Every byte sent over RF today is a target for storage and future decryption.
The Vulnerability: Passive Eavesdropping; adversaries recording encrypted TT&C (Telemetry, Tracking, and Command) data to crack it once a Cryptographically Relevant Quantum Computer (CRQC) is online.
The Technology: Hybrid Key Encapsulation (ML-KEM + ECDH).
Failure Consequence: Total retrospective transparency of all past mission communications.
Progressive Security Actions:
Least Secure: Standard AES-256 with classical Diffie-Hellman key exchange.
Moderate: Pure PQC (ML-KEM) implementation; efficient, but carries “novelty risk” if the algorithm has undiscovered mathematical flaws.
Most Secure: Hybrid KEM; wrapping the session key in both a classical and a PQC layer, combined with SLH-DSA for high-assurance command authentication that doesn’t rely on lattice math.
3. Level 3: The Cryptographic Bus (Internal PQC Orchestration)
Modern “Software-Defined Satellites” (SDS) run multiple virtualized payloads. If the internal bus isn’t quantum-hardened, a compromised low-side sensor could forge a quantum-cracked signature to move laterally to the flight computer.
The Vulnerability: Lateral Key Theft; an attacker exploiting classical weaknesses in internal bus encryption (like SpaceWire or CAN) to pivot between subsystems.
The Technology: PQC-Aware Separation Kernels and Hardware-Accelerated Lattice Math.
Failure Consequence: Intra-satellite “cascading compromise” where a hacked camera takes control of the propulsion system.
Progressive Security Actions:
Least Secure: Flat internal network with no encryption between the bus and the payloads.
Moderate: AES-encrypted internal traffic, but using classical keys that can be extracted via Side-Channel Attacks (SCA).
Most Secure: Implementing Micro-segmentation where every subsystem has a unique ML-KEM identity, with all lattice-based multiplications offloaded to a radiation-hardened PQC FPGA core to maintain zero-latency bus speeds.
4. Level 4: Mission Logic & Crypto-Agility (Behavioral Resilience)
Even with PQC, an adversary might find a vulnerability in the implementation of the algorithm. The mission logic must be “Agile” enough to adapt without losing the asset.
The Vulnerability: Algorithm Obsolescence; a specific PQC standard (like ML-DSA) being “broken” by a new mathematical shortcut, leaving the satellite a sitting duck.
The Technology: Modular Crypto-Agility and AI-Driven Anomaly Detection.
Failure Consequence: Operational paralysis; the satellite is healthy, but its “secure” language is no longer safe to speak.
Progressive Security Actions:
Least Secure: Hard-coded algorithms that cannot be changed without a physical hardware replacement.
Moderate: Over-the-air (OTA) updates for crypto-libraries, but with no secondary “backup” algorithm available in safe mode.
Most Secure: Full Crypto-Agility; the ability to hot-swap between different mathematical primitives (e.g., switching from Lattice-based to Code-based PQC) via a signed uplink, monitored by an onboard AI that flags if a “new” algorithm is causing abnormal power or CPU spikes.
5. Level 5: The Quantum Sunset (Decommissioning & Sanitization)
The “end of life” for a satellite is no longer when the fuel runs out, but when its cryptographic keys are no longer strong enough to protect its “corpse.”
The Vulnerability: Zombie Hijacking; a decommissioned satellite with legacy keys being “woken up” by an adversary using a quantum computer to bypass the dormant authentication.
The Technology: Quantum Crypto-Shredding.
Failure Consequence: A “Ghost” satellite being used as a kinetic weapon or a rogue relay station for illegal transmissions.
Progressive Security Actions:
Least Secure: Simply disabling the transmitter while leaving the classical RSA/ECC keys in the onboard HSM.
Moderate: A software-level wipe of the keys, which may leave “remanence” in certain types of space-grade flash memory.
Most Secure: Zero-Level Crypto-Shredding; an automated trigger that overwrites all PQC and classical key material with random noise, revokes the satellite’s identity on the global PQC Public Key Infrastructure (PKI), and physically “blows” electronic fuses in the RoT before final de-orbit.
II. Which PQC Solutions to Consider?
Selecting a Post-Quantum Cryptography suite for space is a trade-off between cryptographic overhead (larger keys), computational latency (lattice math complexity), and link-budget constraints. Designers must balance these against the mission’s “Data Value Lifetime” using a tiered investment approach.
1. PQC-Ready Hardware Roots of Trust (Physical Layer)
The foundation of quantum resilience is ensuring the satellite’s identity cannot be forged by a quantum computer. This requires a transition from classical RSA/ECC bootloaders to PQC-signed firmware.
The Technology: Stateful Hash-Based Signature (HBS) engines integrated into silicon to verify the initial software load.
Secure Boot & Attestation: The HSM uses NIST-approved LMS (Leighton-Micali Signatures) or XMSS to verify the flight software. These are preferred for hardware because they require very little code to implement and are incredibly resilient.
Implementation Tiers:
Baseline ($): Software-only PQC verification stored in standard flash. High risk of “Quantum Hijacking” if the bootloader memory is tampered with.
Mid-Tier ($$): PQC-Enhanced Secure Elements (e.g., Infineon OPTIGA™ TPM) providing a dedicated vault for ML-KEM and ML-DSA keys.
Strategic ($$$): Quantum-Hardened HSMs (e.g., Rambus RT-640 PQC IP Cores) with Triple Modular Redundancy (TMR). These include dedicated hardware accelerators for polynomial multiplication, ensuring PQC checks don’t delay critical boot times under radiation stress.
Example Providers: Rambus, Infineon Technologies, Xiphos Systems.
2. Lattice-Optimized Separation Kernels (Software Layer)
To prevent a compromised payload from using quantum-cracked credentials to move laterally, the software environment must be strictly partitioned using PQC-aware isolation.
The Technology: Micro-kernels that manage memory in isolated “cells,” where each cell has its own unique PQC-generated identity.
The Challenge: PQC algorithms like ML-DSA (Dilithium) produce much larger signatures than classical ones. The kernel must be optimized to handle these larger memory buffers without crashing.
Implementation Tiers:
Baseline ($): Standard Linux with OpenSSL 3.4+ (PQC enabled). Vulnerable to “noisy neighbor” attacks where PQC math consumes all available CPU cycles.
Mid-Tier ($$): PQC-Ready Real-Time Operating Systems (RTOS) with TEE (Trusted Execution Environment) support to isolate quantum crypto-operations from flight control.
Strategic ($$$): Mathematically Proven Separation Kernels (e.g., seL4 or INTEGRITY-178) that are formally verified to ensure that even if a PQC implementation has a “zero-day” bug, the attacker remains trapped in a single partition.
Example Providers: Green Hills Software, Wind River (VxWorks), DornerWorks (seL4).
3. Quantum-Safe Link Security (Link Layer)
This layer protects against “Harvest Now, Decrypt Later” by ensuring all RF downlinks are wrapped in a quantum-impenetrable shell.
The Technology: Hybrid Key Encapsulation (ML-KEM + ECDH). This combines the speed of classical Elliptic Curve math with the quantum security of lattices.
Implementation Tiers:
Baseline ($): Standard AES-256 using pre-shared static keys. Offers protection against quantum computers (via Grover’s algorithm) but lacks forward secrecy and is difficult to manage at scale.
Mid-Tier ($$): Software-Defined Hybrid PQC on a general-purpose processor. Effective for low-bandwidth TT&C links.
Strategic ($$$): FPGA-Accelerated Hybrid Engines (e.g., Viasat KG-series equivalents). These use dedicated logic gates to process ML-KEM (Kyber) at gigabit speeds, essential for high-resolution Earth Observation (EO) data.
Example Providers: Viasat, Thales Alenia Space, Honeywell (Space).
4. PQC-Aware Zero-Trust Orchestration (Intelligence Layer)
Even with PQC, the logic of a command could be malicious. This layer ensures that every action is verified by multiple “voters” using quantum-secure signatures.
The Technology: Decentralized Ledgers and PQC-Intrusion Detection Systems (IDS).
The Response: If a command is signed with an outdated classical key after the “Quantum Cutover” date, the onboard AI automatically rejects the command and enters a “Cyber Safe State.”
Implementation Tiers:
Baseline ($): Log-based monitoring that flags if classical RSA keys are being used when PQC should be active.
Mid-Tier ($$): Onboard Signature Auditing, where the satellite maintains a list of “Revoked Quantum Keys” to prevent replay attacks using cracked legacy credentials.
Strategic ($$$): Zero-Trust Orchestration (e.g., SpiderOak OrbitSecure). This uses a “Software Guard” to ensure that no single command can move the satellite unless it is signed by multiple geographically dispersed ground stations using PQC ML-DSA signatures.
Example Providers: SpiderOak, Cognitive Space.
III. Example Satellite PQC Strategies
Satellite designers may want to adapt their Post-Quantum Cryptography strategies to fit the specific risk profile, data-value lifetime, and hardware constraints of their mission.
1. The LEO Broadband Megaconstellation (High Volume / Distributed Risk)
Job to be Done: Prevent a “Quantum Worm” from leveraging HNDL (Harvest Now, Decrypt Later) data to compromise the entire mesh network simultaneously.
Applying the Layers:
Silicon Layer (PQC-Attestation): Every satellite uses a Hardware Root of Trust to perform “PQC-Attestation.” Before a new node is allowed into the mesh, it must prove its firmware integrity using an ML-DSA signature that cannot be forged by a quantum adversary.
Link Layer (Hybrid ISL): Inter-satellite links (ISL) use Hybrid Key Encapsulation. By combining classical AES-256 with ML-KEM, the constellation ensures that if one algorithm is compromised, the mesh remains opaque to eavesdroppers.
Bus Layer (Quantum-Isolated Comm-Sandbox): Customer data packets are processed in a PQC-encrypted container. Even if a packet contains a “quantum-crack” exploit for a legacy protocol, it is logically isolated from the flight computer via an seL4 microkernel.
Logic Layer (Consensus Revocation): If a satellite begins broadcasting packets with invalid PQC signatures, neighboring nodes use a Byzantine Fault Tolerant voting mechanism to revoke its keys and physically ignore its RF output.
Example Vulnerability: Mesh-Wide Key Compromise. An attacker using a quantum computer to crack a single master bridge-key to intercept global traffic.
2. The Strategic Military Reconnaissance Asset (National Interest / High Stealth)
Job to be Done: Defeat state-level “Quantum Supremacy” and protect high-classification imagery for 30+ years.
Applying the Layers:
Silicon Layer (Stateful HBS): Uses LMS/XMSS signatures burned into the silicon for Secure Boot. These are “mathematically “certain” PQC primitives, ensuring the satellite’s core identity is quantum-immutable for its entire lifespan.
Link Layer (The Dual-Shield): Employs a combination of Quantum Key Distribution (QKD) for physical security and SLH-DSA for hash-based authentication. This “physics + math” approach ensures that even an “impossible” quantum breakthrough cannot crack the link.
Bus Layer (Air-Gapped Crypto-Cores): The PQC encryption engines are physically separated from the main processor. A compromised SIGINT payload cannot “sniff” the lattice-multiplication cycles of the flight controller’s PQC module.
Logic Layer (Quantum Anomaly Detection): The onboard AI monitors for Quantum-Side-Channel Attacks, specifically looking for unusual power fluctuations that might occur if an adversary is trying to “fault” a lattice-based polynomial multiplication.
Example Vulnerability: Retrospective Decryption. A foreign power storing 2026 intelligence to reveal troop movements in 2030 using a CRQC (Cryptographically Relevant Quantum Computer).
3. The University 3U Research CubeSat (Low Budget / Educational)
Job to be Done: Provide “Good Enough” quantum resistance without expensive dedicated hardware.
Applying the Layers:
Silicon Layer (Software-PQC Watchdog): Lacks an HSM; instead, it uses a PQC-Library (like liboqs) running on a standard ARM Cortex-M4. A hardware watchdog forces a reset if the heavy lattice math causes a system hang.
Link Layer (NIST-Selected Software Implementation): Implements ML-KEM-512 (the lightest version) in software. While slower, it protects the student research data from basic “Harvest Now” threats.
Bus Layer (Ephemeral PQC Keys): To save memory, the satellite generates a new PQC keypair for every ground pass. Old keys are immediately overwritten (”Crypto-shredded”) in RAM to minimize the attack surface.
Logic Layer (Time-Locked PQC Handshake): The satellite only attempts the heavy PQC key exchange during a specific 5-minute window of its orbit, conserving battery for the rest of the mission.
Example Vulnerability: Resource Exhaustion. An adversary spamming complex PQC handshake requests to drain the CubeSat’s limited battery.
4. The 15-Year GEO Telecommunications Hub (High Capital / High Longevity)
Job to be Done: Future-proof a multi-billion dollar asset against the “Quantum Sunset” of the late 2030s.
Applying the Layers:
Silicon Layer (Crypto-Agility Modules): Carries Field-Programmable PQC Engines. If NIST updates the ML-KEM standards in 2030, the FPGA can be reconfigured in orbit to support the new math without a hardware swap.
Link Layer (Multi-Algorithm Hybrid): Uses a “Triple-Wrap” strategy; AES-256 + ECC + ML-KEM. This provides the highest possible assurance that customer telecasts remain private for the next two decades.
Bus Layer (Protocol Translation Isolation): A dedicated “PQC-Gateway” handles all external PQC handshakes, translating them into simpler internal AES-GCM commands for the 15-year-old legacy hardware on the transponder bus.
Logic Layer (Golden Image PQC): Maintains an immutable “Quantum-Safe Recovery Image” in ROM. If the main software is ever compromised by a future exploit, the ground can trigger a hard-reset to a baseline PQC-authenticated state.
Example Vulnerability: Key Aging. A 2026-era PQC key becoming “weak” by 2040 due to unforeseen advances in quantum cryptanalysis.
5. The “VLEO” Imaging Skimmer (Atmospheric Combat / Fly-or-Die)
Job to be Done: Ensure that PQC-authenticated commands for high-cadence thruster firing never suffer from “Lattice Latency.”
Applying the Layers:
Silicon Layer (Low-Latency PQC Cores): Uses ultra-fast Lattice-Math Hardware Accelerators. These cores ensure that the 2,420-byte ML-DSA signatures are verified in microseconds, preventing propulsion lag.
Link Layer (Stream-Authenticated PQC): Rather than a slow handshake, it uses Stateful Hash-Signatures on every packet. This ensures that every “Fire Thruster” command is verified as quantum-authentic in real-time.
Bus Layer (Deterministic Priority): The internal bus uses Hardware-Level Rate Limiting. Even if a payload is trying to perform a heavy “Quantum-Search” attack on internal keys, the propulsion commands are guaranteed 99% of the bus bandwidth.
Logic Layer (Kinetic PQC Watchdog): An AI cross-references PQC-signed commands with the satellite’s physical state. If a “Quantum-Valid” command tells the satellite to de-orbit, the AI rejects it if the atmospheric drag sensors don’t justify the move.
Example Vulnerability: Jitter-Induced Decay. Forcing the CPU to focus on heavy PQC math, causing a 10ms delay in thruster timing that results in the satellite burning up in the atmosphere.
VI. Upgrading In-Orbit Assets (PQC Retrofitting)
1. The “Software-Agile” Path (Easiest / Most Common)
This applies to modern, Software-Defined Satellites (SDS) launched within the last 3–5 years that possess high-end FPGAs or powerful general-purpose processors (e.g., ARM Cortex-A series).
The Strategy: OTA (Over-the-Air) Cryptographic Injection.
The Action: Operators push a firmware update that includes highly optimized PQC libraries (like liboqs).
The Compromise: Because PQC algorithms like ML-KEM (Kyber) have larger public keys (~800–1600 bytes vs. RSA’s 256 bytes), the operator must sacrifice a small portion of the communication bandwidth to accommodate the larger handshake overhead.
The Result: The satellite becomes “Hybrid-Ready,” using classical encryption for speed and PQC for long-term quantum resistance.
Example Vendors:
QuSecure: Their QuProtect software is designed for orchestrated PQC deployments across diverse satellite nodes.
Sandia National Laboratories: Pioneers in the Open Quantum Safe (OQS) project, providing the foundational liboqs library used in satellite firmware patches.
Cognizant: May be able tp provide integration services for deploying PQC libraries into existing Ground-to-Space software stacks.
2. The “Resource-Constrained” Path (Moderate Difficulty)
This applies to older satellites or CubeSats with limited RAM (under 256KB) and slow CPUs (M-class microcontrollers). These assets weren’t designed to handle the complex lattice-math or the large signatures of NIST-standard PQC.
The Strategy: Thin-Slicing & Stateful Hashing.
The Action: Instead of the full NIST suite, developers could implement Stateful Hash-Based Signatures (LMS/XMSS). These algorithms have a very small code footprint and low RAM requirements, making them ideal for “thin” hardware.
The Compromise: Stateful signatures require the satellite to “remember” which index of a signature tree it has used. If the satellite reboots and “forgets” its state, the security is compromised. This requires writing to non-volatile memory (Flash) with every single command sent, which can wear out the hardware over time.
The Result: A “Quantum-Safe-Lite” asset that is protected against signature forgery but may still be vulnerable to HNDL (Harvest Now, Decrypt Later) on the data link.
Example Vendors:
WolfSSL: Offers lightweight, NIST-compliant PQC implementations specifically optimized for resource-constrained embedded systems in space.
ISARA: Specialized in “Agile” crypto-toolkits that allow for the deployment of stateful hash signatures on older processor architectures.
PQShield: Provides high-assurance PQC implementations tailored for low-power, radiation-hardened microcontrollers.
3. The “Legacy-Hardened” Path (Impossible / End-of-Life)
This applies to satellites with ASIC-based (Application Specific Integrated Circuit) encryption. These chips are “hard-wired” for RSA or AES and cannot be changed via software.
The Strategy: Ground-Segment Tunneling & Risk Isolation.
The Action: Since the satellite itself cannot be upgraded, the operator must “harden the ground.” All data coming from the legacy satellite is immediately wrapped in a PQC tunnel the millisecond it hits the ground station.
The Compromise: The link between the satellite and the ground remains “Quantum-Vulnerable.” The operator must accept that an adversary could record this traffic today and crack it in 2030.
The Result: The asset is treated as “Untrusted.” It is isolated from the rest of the constellation to ensure its classical weakness doesn’t allow for lateral movement into newer, PQC-secured satellites.
Example Vendors:
Viasat: Offers “PQC-Gateway” hardware for ground stations that can wrap legacy satellite streams in quantum-secure tunnels.
SpiderOak: Their OrbitSecure platform utilizes a Zero-Trust architecture to isolate these “untrusted” legacy assets within a wider, secured network.
Thales Alenia Space: Provides mission-management systems that can segment “Quantum-Vulnerable” legacy satellites into isolated VLANs to protect fleet integrity.
V. Potential Opportunities for New Innovators
The shift to Post-Quantum Cryptography (PQC) is creating a new “Secure Space Economy.” As legacy systems become obsolete, innovators have a unique window to build the foundational secure infrastructure of the future.
1. Level 1: The Silicon Foundation (PQC-Hardened RoT)
Standard satellite chips are optimized for legacy math. The next generation of space hardware requires dedicated PQC acceleration in silicon.
The Opportunity: Developing “Lattice-Native” Hardware Security Modules (HSMs) that can survive both cosmic radiation and quantum cryptanalysis.
Innovation Focus:
Radiation-Hardened PQC Accelerators: Engineering RISC-V or FPGA-based cores optimized for the heavy polynomial multiplications in ML-KEM and ML-DSA.
Side-Channel Resistant Logic: Designing silicon that masks the power and thermal “noise” of PQC math, preventing adversaries from using side-channel attacks to extract private keys.
PUF-Linked PQC Identities: Utilizing Physically Unclonable Functions (PUF) to generate quantum-resistant keys that are physically unique to the individual chip’s silicon structure.
Example Innovators: Rambus (Security IP), Infineon (Secure Elements), Xiphos Systems (Space Computing).
2. Level 2: The Link Segment (Quantum-Safe Gateways)
Ground-to-space links are currently the most vulnerable to “Harvest Now, Decrypt Later.” Innovators can build the secure “bridges” that protect this high-risk segment.
The Opportunity: Developing “Hybrid PQC/QKD Gateways”; modems that combine mathematical PQC with physical Quantum Key Distribution for ultra-high-value links.
Innovation Focus:
PQC-Overlay Modems: Software-defined modems that wrap existing satellite uplinks in an ML-KEM shell, allowing legacy constellations to become quantum-safe without hardware launches.
Low-SWaP Lasercom PQC: Integrating PQC authentication into optical (laser) communication terminals to ensure that even at multi-gigabit speeds, every packet is quantum-verified.
Zero-Knowledge Link Attestation: Protocols that allow a ground station to verify a satellite’s security posture without the satellite ever revealing its internal key architecture.
Example Innovators: Mynaric (Lasercom), Viasat (Link Security), QuSecure (PQC Software).
3. Level 3: The Internal Network (Secure Bus Middleware)
Modern satellites are “Data Centers in Orbit.” Innovators can build the internal firewalls that prevent lateral movement once a single payload is compromised.
The Innovation: PQC-Aware Separation Kernels and Bus Guardrails.
The Opportunity: Developing the “Secure Orbital OS”; a middleware layer that creates quantum-isolated “sandboxes” for every onboard subsystem (Propulsion, Payload, Navigation).
Innovation Focus:
Micro-Segmented PQC Buses: Software that assigns a unique, quantum-resistant identity to every sensor on the CAN or SpaceWire bus, preventing a “hacked camera” from talking to the “thruster.”
Lattice-Optimized RTOS: Real-time operating systems (RTOS) that manage the large 2KB+ PQC signatures without causing timing jitter in critical flight controls.
Bus-Level IDS (Intrusion Detection): Onboard agents that monitor internal traffic for the high-computational signatures of unauthorized quantum-key searches.
Example Innovators: Green Hills Software (RTOS), seL4 Foundation (Microkernels), DornerWorks (Virtualization).
4. Level 4: Mission Logic (Behavioral & Kinetic PQC)
Even perfect encryption cannot stop a “Living-off-the-Land” attack. The opportunity lies in ensuring the intent of a command is safe, even if it is signed with a valid PQC key.
The Opportunity: Developing “Kinetic Safety Oracles”; onboard AI that cross-references PQC-signed commands against the physical laws of orbital mechanics.
Innovation Focus:
Quorum-Based Command Logic: Systems requiring “Multi-Signature” PQC approval from geographically dispersed ground stations before executing high-risk maneuvers.
PQC-Authenticated AI Watchdogs: Onboard Edge-AI that continuously verifies the satellite’s behavior against its mission plan, triggering a hardware-locked “Safe State” if a command violates kinetic limits.
Tamper-Proof Logic Logs: Using hash-based signatures to create an immutable log of every command, providing the forensic evidence needed for insurance claims after a “soft-kill” attempt.
Example Innovators: SpiderOak (Zero-Trust), Cognitive Space (Mission Ops), Privateer (Space Data).
5. Level 5: The Terminal Phase (Post-Mission Stewardship)
Security must last beyond the mission’s life to prevent “Zombie” hijacking. Innovators can provide the “Digital Burial” services for old assets.
The Opportunity: Developing “Remote PQC-Shredding” and Sustainability-Linked Security Bonds.
Innovation Focus:
Automated Master Key Wipe: Hardware triggers that use PQC-authenticated “Death Certificates” to permanently overwrite HSM keys before final power-down.
PQC-Revocation Oracles: Global registries that broadcast the “retirement” of a satellite’s identity, ensuring its legacy keys can never be reused by an adversary in the future.
Quantum-Hardened De-orbiting Kits: Standardized bolt-on modules that provide an independent, PQC-secured command link specifically for de-orbiting non-functional assets.
Example Innovators: Astroscale (Debris Removal), AstroPledge (Crypto-Legislation), LeoLabs (Risk Monitoring).